Mar 12, 2026 | CDM, Continuous Diagnostics & Mitigation, Cybersecurity, SIEM, Technology News
OT systems, which govern essential shipboard functions such as navigation, propulsion, and cargo handling, remain a major focus for attackers. Many of these systems rely on outdated software and lack modern cybersecurity measures, making them highly susceptible to breaches. Additionally, the growing interconnectivity of IT and OT systems introduces cascading risks, where a single breach can disrupt both operational and digital environments.

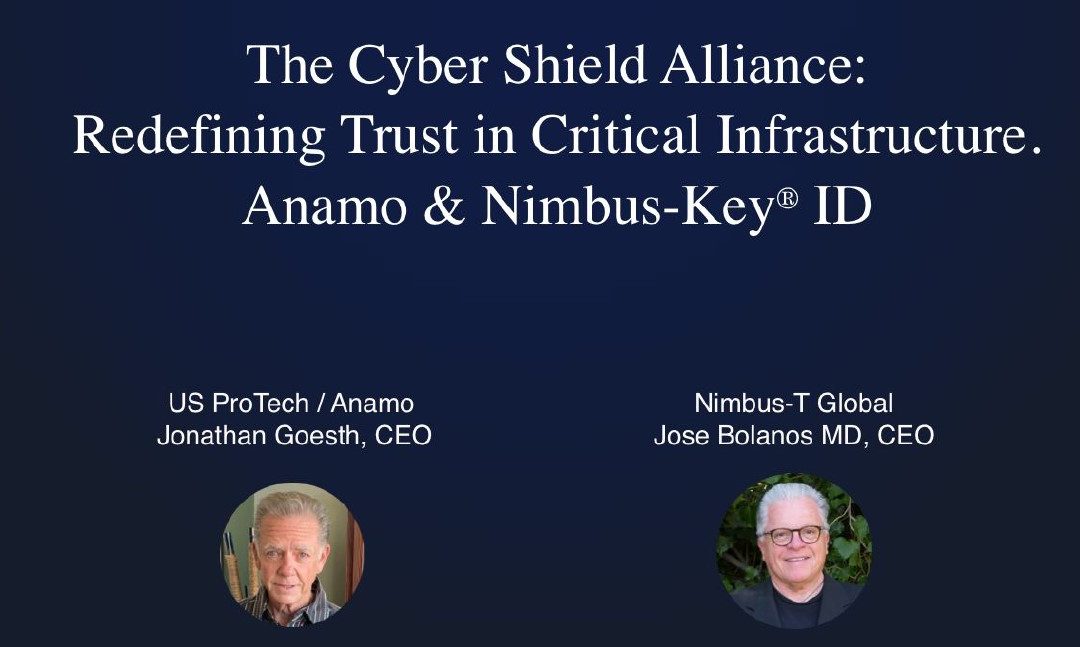
Nov 13, 2025 | Critical Infrastructure, Cybersecurity
“Managing the Cybersecurity of the largest Ports Critical Infrastructure in America is no small matter” stated Goetsch. Membership to the Ports Cybersecurity Subcommittee for the protection of Critical Infrastructure is intentionally kept to a small group of legislators and subject matter experts (SME’s) and Federal staff members from the CISA, DHS, the FBI, Port Authorities, and key Port tenants. The So-Cal based Subcommittee focusses on the smooth, safe and secure delivery of what is essential to the daily operations in Southern California.
Nov 13, 2025 | Critical Infrastructure, Cybersecurity, Technology News
Dear Cyber Professional and Team Member: October and November 2025 marked another critical and active period in the vulnerability landscape, with over 3,700 new CVEs published and 5,200 modified entries as critical flaws surged across software, hardware, and...
Oct 14, 2025 | Continuous Diagnostics & Mitigation, SIEM, Technology News
Security Incident Event Management (SIEM) is a saturated industry with over 30 notable businesses specializing in the correlation of Cybersecurity threat analytics, but only one of those companies focus on Host-Based devices rather than Network-Based events. The problem for industry is insatiable rise of Hackers and that they have proven that they are skilled as they continuously usurp the current “Tech-Stack” of modern Cybersecurity tools, services, and protections, used by Mid-Market Corporations and Enterprises today.
Oct 14, 2025 | Continuous Diagnostics & Mitigation, Critical Infrastructure, Cybersecurity, Technology News
Red Hat admitted it was breached:
But have they failed to disclose what really happened? Maybe Red Hat is just going to wait that out, you know, just like the US Dept. of Treasury did after they were breached, then lied about the extent of the Hack, until the truth was realized and disclosed.
Oh well… here we go again.
Sep 19, 2025 | Breach, Critical Infrastructure, Cybersecurity, SIEM, Technology News
Still using 20+ Yr old Splunk or another Log-Based SIEM? While obvious, it’s 2025, and there’s been new SIEM technology available for years! It’s Anamo, a log-less SIEM that’s eliminating traditional “Blind Spots” and various anomalies related to System-Based Indicators of Attack (IoA”s), Modifications of Users, Permissions, Ports and Transactions… and much more! Anamo is named after its ability to rapidly identify Host-Based attack vectors and other Indicators of Compromise (IoC’s) where all other Network-based SIEMs remain blind.
Jul 21, 2025 | Breach, CDM, CISA, Critical Infrastructure, Cybersecurity, DHS, IoT, IT, OT
China probably currently represents the broadest, most active, and persistent cyber espionage threat to the U.S. government and private sector networks. China’s cyber pursuits and its industry’s export of related technologies increase the threats of aggressive cyber operations against the U.S. homeland, suppression of the free flow of information in cyberspace -such as U.S. web content- that Beijing views as threatening to the CCP’s hold on power, and the expansion of technology-driven authoritarianism globally.

Jul 21, 2025 | CDM, CISA, Critical Infrastructure, Cyber Command, Cybersecurity, DHS, Technology News, US Cyber Challenge
The United States Cyber Command (USCYBERCOM) has published its Command Challenge Problems to provide industry partners with clear insight into the critical technology areas where innovative solutions are needed. As the cyber threat landscape continues to evolve, the Department of Defense must stay ahead of adversaries by integrating cutting-edge capabilities in cybersecurity, artificial intelligence, network defense, and other key domains. By outlining these challenge problems, USCYBERCOM seeks to foster collaboration with industry leaders, ensuring that the nation’s cyber forces are equipped with the most advanced tools to protect national security interests.
Jul 21, 2025 | Breach, CDM, Channel, Channel Partners, CISA, Critical Infrastructure, Cybersecurity, DHS, IoT, IT, OT
ANAMO delivers near real-time risk information based upon next generation cybersecurity technologies that provide a unique and comprehensive view of four critical areas of cyber-hygiene including:
Software & Hardware Vulnerability Management of the OS, Patch and Kernel.
Attack-Surface Management from the Workstation and Server, to Cloud Containers.
Objective-Based Behavioral Risk Analytics of Users, Permissions, File Tree, and Ports.
A Gathering of Deep Data Forensics for Finite and Comprehensive, Global Reporting.
See all major operating systems (Windows, Linux, macOS) across the enterprise in near real-time.

Jun 29, 2025 | SMB Technology, SMB Technology, SMB Technology, SMB Technology, Technology News
This year, all eyes will once again be on DEFCON (https://defcon.org/index.html). DEFCON is where the world’s elite Hackers come to play under the heat of the Las Vegas sun, and by night, well that’s Vegas! Still, inside the cool dark ballrooms of the Convention...
Page 1 of 3212345...102030...»Last »