Aug 20, 2024 | CDM, Continuous Diagnostics & Mitigation, Technology News
Have you been searching for the right opportunity where your professional selling skills and honorable work ethic could be “transformative” and at the same time be transformed into a position where real equity would be on the table for you? If so, then you have come to the right place and found Anamo.

Aug 15, 2024 | CDM, Continuous Diagnostics & Mitigation, Technology News
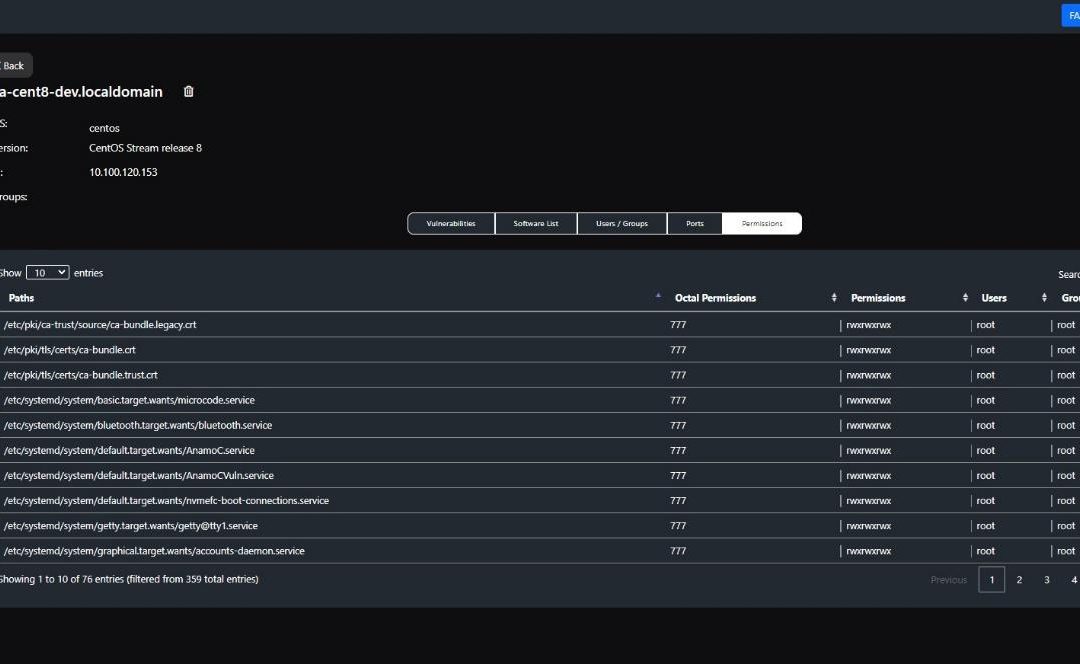
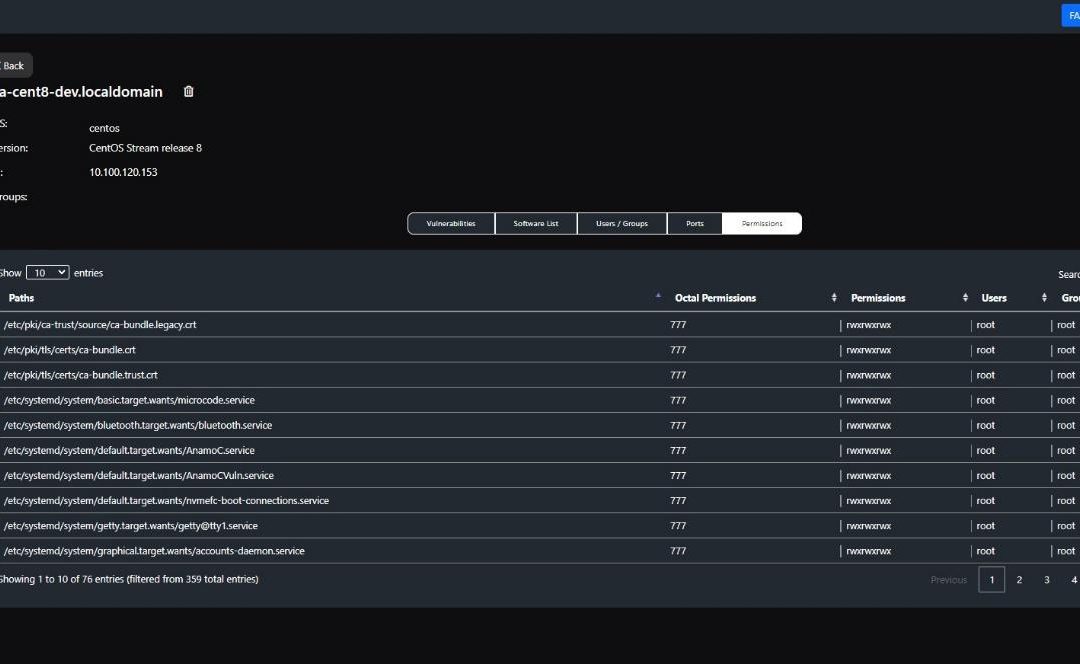
Today, over 300 Federal Agencies have fully adopted the CISA and DHS “Continuous Diagnostics and Mitigation” (CDM) Cybersecurity program as an essential, core attribute to their Cybersecurity Defense operations. The reason is compelling, with the emergence of CDM and its adoption of Generative Artificial Intelligence (AI), it presents a promising avenue to fortify cybersecurity defenses which enhance the management, monitoring and mitigation of risk and vulnerabilities across and entire ecosystem. Anamo is CDM and its leading the charge in the rapid adoption of AI and predictive risk extrapolation.

Aug 14, 2024 | SMB Technology, SMB Technology, SMB Technology, SMB Technology, Technology News
As we saw two weeks ago, our entire world is dependent on technology. The global technology outage precipitated by a faulty software update rollout by Crowdstrike illustrates how a small problem can have enormous repercussions. The recovery will likely be difficult and expensive for many companies but especially for small to medium-size businesses. Read on to learn about how a technology advisor can help your company mitigate damage from and even prevent technical issues

Aug 5, 2024 | SMB Technology, SMB Technology, SMB Technology, SMB Technology, Technology News
Doing business in today’s world doesn’t come without risk. Anything can happen, from a brief power failure resulting in two hours of downtime, to a days-long global technology outage precipitated by a CrowdStrike software update. How will you know what risks your business is most subject to, and how to mitigate those risks? Read on to find out what types of risks can threaten your company, and how to protect yourself.
Jul 28, 2024 | SMB Technology, SMB Technology, SMB Technology, SMB Technology, Technology News
A week ago, Cloudstrike push a software update that will forever change business as usual at the Cybersecurity giant… and the fallout will most likely result in a decade of litigation. The suspected cause of the error by Cloudstrike may be found in the incorrect application of standard CI/CD controls.

Jul 16, 2024 | SMB Technology, SMB Technology, SMB Technology, SMB Technology, Technology News
In 2020, the way people worked changed, likely for good. Instead of being in the office most of the time, employees worked at home. Although some workers have come back to the office, hybrid work is here to stay. Secure Access Service Edge (SASE), pronounced “sassy”) is ideal for hybrid work, with its cloud-native architecture, centralized access policies and support of access based on device identity. Read on to learn more about this architecture and what it can bring to hybrid offices.

Jul 15, 2024 | SMB Technology, SMB Technology, SMB Technology, SMB Technology, Technology News
Communications and collaboration are vital to your company’s operations and success. But how do you know if your spending is effectively allocated? Read on to learn about the role of a telecommunications expense audit in shaping up your telco budget

Jul 9, 2024 | SMB Technology, SMB Technology, SMB Technology, SMB Technology, Technology News
What will your company do with artificial intelligence, now that it’s a key technological trend? Artificial intelligence (AI, for short) holds the potential to revolutionize how your business meets its goals. Fueled by the natural language model of generative AI, automation of processes, data analysis, and streamlining tasks have all helped businesses work more efficiently. Read on to learn more about specific use cases for different aspects of your business.
Jul 4, 2024 | SMB Technology, SMB Technology, SMB Technology, SMB Technology, Technology News
There’s never a bad time to examine your company’s cybersecurity posture, and even improve your strategy. Threats abound, including security incidents resulting from weak passwords, phishing attacks, and the lack of strong authentication. Read on to learn how you can assess and improve your preparedness for security incidents–it’s not if, but when.

Jun 20, 2024 | SMB Technology, Technology News
The Quantum Leap in Cryptography The National Institute of Standards and Technology (NIST) is on the brink of a groundbreaking release, poised to unveil its post-quantum cryptography (PQC) guidance during the week of August 12th. But will it get swept away in...