Compare
US ProSoc
Solutions
Compare US ProSOC Solutions
US ProTech delivers a highly robust Security Operations Center (SOC) as a service, built upon the ELK Stack. Simply stated, the “ELK” (Elasticsearch, Logstash & Kibana) Stack is opensource, more comprehensive, more powerful, and the better globally supported SIEM product available today. US ProTech delivers two unique solutions.
US ProTech ALSO OFFERS A 100% CUSTOM BUILT “ON-SITE ELK STACK” AS A PROFESSIONAL MANAGED SERVICE FOR CLIENTS WITH HIGHLY SPECIALIZED REQUIRMENTS. CONTACT US ABOUT OUR PLATINUM ELK -STACK SERVICE.
US ProSOC: WHAT IS IT?
US ProSOC is a fully managed cloud-based, virtual Security Operations Center empowering clients with sophisticated Cybersecurity data analytics, forensics, and enterprise-grade SIEM for security monitoring and remediation guidance.
The ELK; Using the ELK as the SOC Core for Cybersecurity Intelligence, US ProSOC rapidly deploys from the cloud (or optionally on an internal dedicated device), adopting standard VPM security controls and were desired, other security protocols maintaining any number of regulatory compliance requirements. Working together, these consolidate multiple automated and curated threat intelligence data sources into dashboards, while our global network of SOC’s provides 24/7 analysis, alert notifications, and advanced remediation guidance. US ProSOC gives its clients the ability to deliver a fully managed version of an enterprise-level advanced cybersecurity capability referred to as “SIEM” or Security Incident Event Management.
FEATURES
Automatic incident reporting
The US ProSOC ELK/VM and lightweight monitoring agent instantly uploads logs and other critical Cybersecurity data to the cloud, enabling quick response and support.
Endpoint monitoring
Monitoring both “software” and “applications,” US ProSOC will detect known security vulnerabilities and suspicious activity of macOS, Linux and both Windows Server and Workstations.
Remediation suggestions
Alerts are accompanied by suggestions for remediating the cause of security events.
Detailed analytics
US ProSOC provides tools and analytics to gain insight on incidents, and help identify weaknesses, improve response times, and optimize workflow.
BENEFITS
Easy to deploy. Built to easily get running on customer endpoints via a simple MSI installer.
Non-invasive. US ProSOC uses a background process, easy to integrate into your existing services with minimal resource demand.
The US ProSOC management portal provides secure and controlled access via MFA or SSO.
Client can opt for On-Site data storage within its own environment or select US ProSOC secured off-site data storage for Disaster Recovery, Compliance, or another requirement.
DIFFERENTIATORS
Right sizing the SOC service, our clients can select on-site or off-site local file system data storage to accommodate their own regulatory requirements or budgetary considerations.
100% of all local file system and endpoint network traffic inspected for suspicious and/or malicious activity. This data is gathered and kept for forensic purposes.
Roll-based portal access provides for layered viewing of all endpoints.
Flexible alerting — use in-product alerting or integrate into an existing alerting system.
WHAT ROLLOUT OPTIONS EXIST?
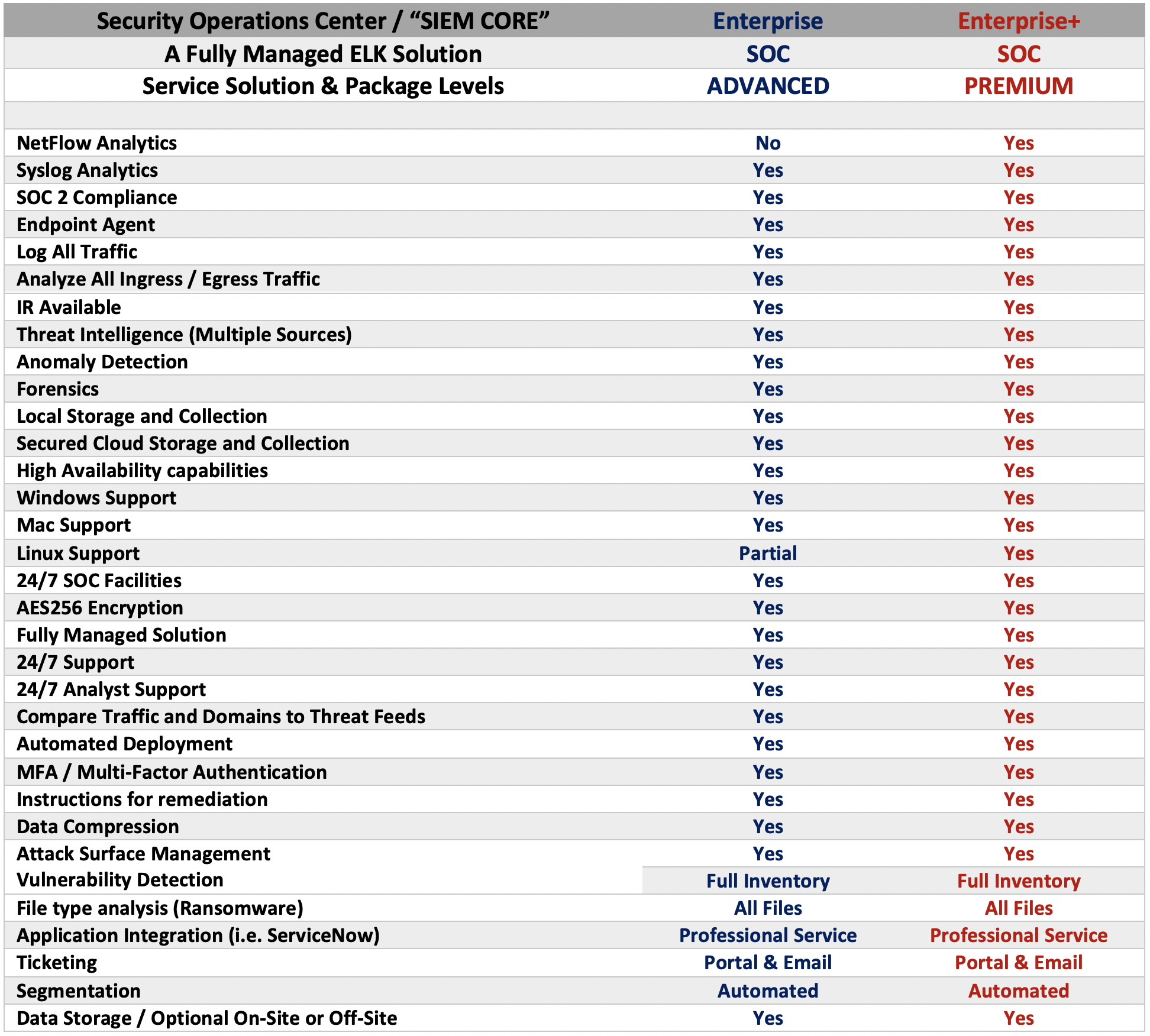
The Two Enterprise Plans
The Choices are yours:
Enterprise clients enjoy an Always-On 24/7/365 SOC, delivering a multitude of US ProSOC service capabilities. This service is available globally, supported in multiple languages, provisioned, and managed within four SOC-Certified Data Centers with a seasoned and experienced Cybersecurity team. Client choices include off-premises or a combination of on-prem and off-prem resources. In addition to these US ProTech also offers an on-site Beta option.
