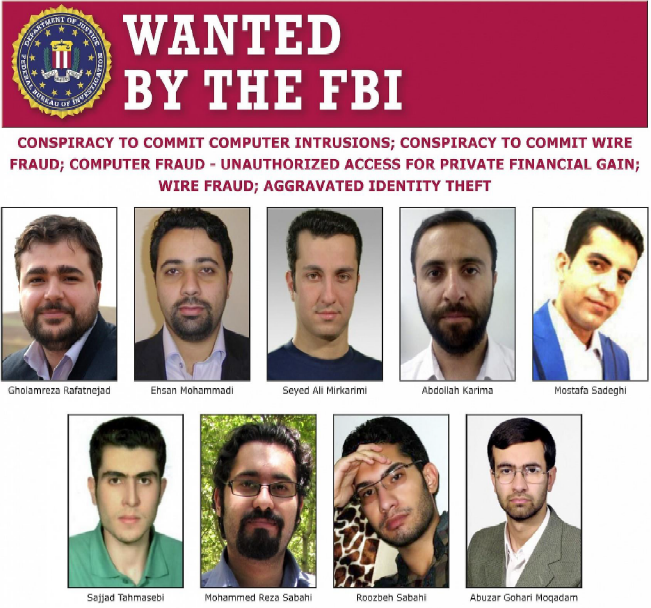
What does the Nation of Iran, 144 American Universities and US ProTech have in common? Let’s answer that question right now and discuss “how did they do it and what did they get.” Sure, some of the questions we’ll address are technically sophisticated but the weaknesses exploited could also be considered criminally negligent. To provide some background, let’s have a look at the Iranian Mabna Team who you’ll learn are a collective of government sponsored cyber-criminals, aka – The Bad Actors.
Examples of Mabna Team’s work include a coordinated effort to hack 100’s of Universities around the globe to steal intellectual property, scientific data and other confidential information. According to what US ProTech derived from an FBI investigation, this group of malicious cyber actors are working for the Iran-based Mabna Institute. They have been conducting broadly targeted password spray attacks against organizations in the United States and abroad.
DOJ specifically targeted the Iran-based Mabna Institute, which it says was founded in 2013 “to assist Iranian universities and scientific and research organizations in stealing access to non-Iranian scientific resources. The problem remains however that victims of Mabna often lack multi-factor authentication (MFA), an active penetration testing program, lack preventative network activity alerts, and allow easy-to-guess passwords.
What will it take before we have a society which is compelled to use standard security measures that would have avoided these breaches (i.e. NIST 800, CDM, etc.)? The link here is that Mabna exploits hard to detect lateral and vertical application moves known as a “pivot”. Ironically, Anamo (www.Anamo.io), already monitors, manages and alerts upon any “pivot” that a hacker might use and the application is commercially available. When combined with MFA and a good Password policy and regular pen-testing, nearly 100% of these hacks could have been avoided” said Goetsch, a 19-year veteran White-Hat, America cybersecurity expert and forensic analyst. “These nine Bad-Guys are true “Enemies of the State.” added Goetsch, CEO of US ProTech and Anamo (a Cybersecurity services and Software development organization respectively). “But we also need to take care here at home and to do a better job of protecting data, training workers and implementing solutions that monitor, track, alert and stop hackers with Continuous Detection & Mitigation (CDM). Anamo has been short-listed by the U.S. Government and addresses Phase II and Phase III CDM objectives.
“Just the facts Ma’am.” Over the course of four years, prosecutors say, hackers working for the Mabna Institute stole at least 31 terabytes of data from 144 American universities, totaling $3.4 billion in “IP (intellectual property). The group also cracked into 176 foreign universities, DOJ said. “The government of Iran systematically and methodically hacked into our country’s computer networks with the intent to steal as much information as possible,” Berman told reporters at a Friday press conference. According to court documents, the hackers compromised these systems by sending emails to professors, posing as other professors, that tricked targets into giving up their login credentials.
More can be read about this matter here: