CONFIDENTLY DELIVER, SECURE MANAGE & AUDIT YOUR NETWORK INFRASTRUCTURE, TODAY!
Would you “know” if an adversary was navigating within your computing network within minutes?
US ProTech’s Soc as a Service is a comprehensive suite of capabilities and services and offers constant analysis of your network traffic while monitoring your cybersecurity risk 24/7/365. Thanks to this, you can discover how your network stands from an operational and security point of view and deliver Role-Based reporting from Line-Staff to the C-Suite. Our specialists audit your environment and deliver a comprehensive technical and managerial report including recommendations on what should be improved. Access to our Dashboard and Alert notification is standard along with comprehensive reporting.
Now, consider NetFlow, the ELK Stack, BRO, auditability and cybersecurity forensic data collection. It’s our goal to detect anomalies, existing security risks, propose optimal network capacity distribution, identify critical points, detect internal and external attacks and identify which users and services consume most network performance. US ProTech tools provide “constant-audit” a very beneficial source of information for network engineers, security experts and application specialists. The analysis is all carried out by the US ProTech SOC as a Service. We summarize the structure and characteristics of your traffic and we identify anomalies (with Anamo.io) and malicious traffic such as port scanning, attacks on network services, illegal file sharing, botnets etc. The specialists also focus on operational issues such as wrong configurations and unavailability of services.
Considering: Security Operations Center (SOC) as a Service
Have you heard? The DHS has rolled out its newest cybersecurity program and chances are… you’ve never heard about it. However, if you have heard about “CDM” that might make you a cybersecurity expert.
US ProTech SOC AS A Service Also Includes End-Point Protection:
CYBER TERRORIST NETWORK CONNECTION
ADVANCED BREACH DETECTION (TTPS)
SUSPICIOUS EVENT LOG MONITOR
SUSPICIOUS NETWORK SERVICES
SUSPICIOUS TOOLS
CRYPTOCURRENCY MINING DETECTION
THREAT INTELLIGENCE FEEDS
ON-DEMAND MALWARE ANALYZER
ON-DEMAND THREAT HUNTING
PASSIVE THREAT HUNTING
SYSTEM PROCESS VERIFIER
MALICIOUS FILE DETECTION
Question for the CEO, CIO and CISO: “If you could have a highly trained and experience Team of cybersecurity professionals working 24 hour a day for your organizations benefit while using today’s most modern CDM tools, would you sleep better? What if you could access deep informatics, tiered-responsibility reporting and a trusted process for alert notification and remediation, and it all came bundled in a single affordable Operational Expense, would you be interested to learn more about such an outsourced service? (askes, Jonathan Goetsch, CEO of US ProTech, Inc.) This question is addressed below and supported by one of the only companies in the entire cybersecurity space of America with a government validation under NIST 800-53R4.
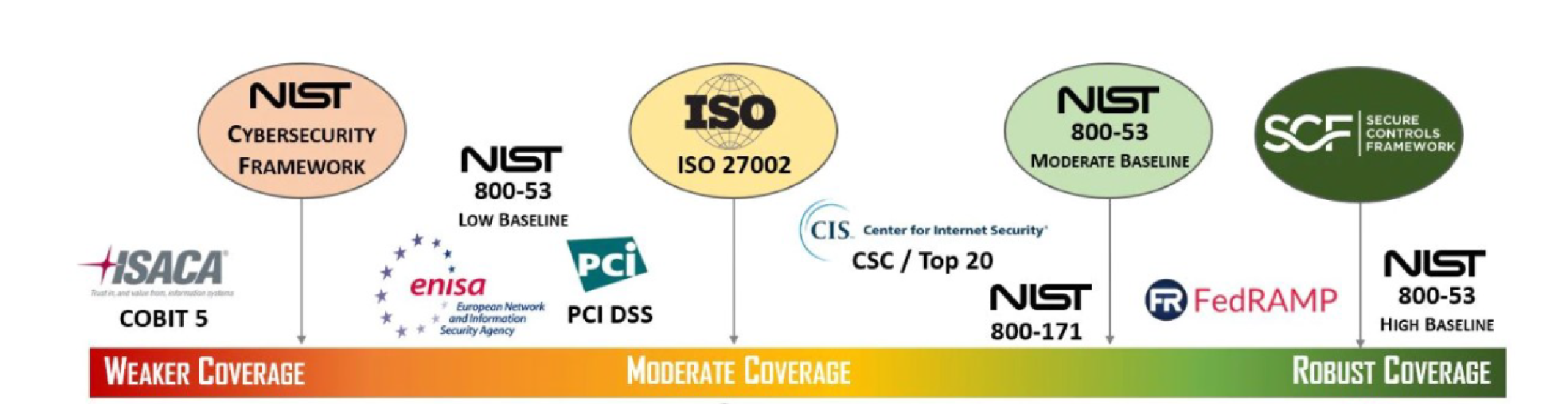
Selecting a compliance standard is essential in today’s complex security landscape: Since 2007 US ProTech has embraced NIST 800 as its base-line Cybersecurity platform and provides clients with the highest caliber of data within the United States, specifically, US ProTech’s vulnerability and risk scanning process has been Validated by the U.S. Department of Commerce to exceed the High-Impact Baseline Security Control standards of NIST 800-53R4 (shown below at the far right).
NIST 800, SCAP and the NVD: The US ProTech NIST 800-53 based framework cybersecurity process, considered superior to all other standards, also accommodates the requirements for Security Content Automation Protocol (SCAP) providing exact target analytics, trend analytics and the capability to examine, and re-examine a single attack vector or any group of vectors while providing comparative data and recommended remediation per the directives given and updated by the National Vulnerability Database (NVD).
*CDM and the Anamo.io Platform: Furthermore, proprietary software platforms developed by US ProTech address the primary objectives of today’s most advance cybersecurity programs within the U. S. Government (Department of Homeland Security) known as “Continuous Diagnostics and Mitigation” (CDM). The Anamo.io platform has been skillfully developed by advanced cybersecurity engineers to address the CDM program directives under Phases 2, 3 and 4. Anamo.io is the only commercially available Real-Time cybersecurity product that pushes insider-threat analytics and critical software vulnerability data to a live dashboard while collecting essential judicial prosecutorial forensic information. Using the ELK Stack and its integrated SIEM platform, US ProTech delivers its Security Operations Center (SOC) as a Service, providing a comprehensive solution to this complex landscape.
The US ProTech SOC as a Service / Overview:
US ProTech offers the only deliverable SOC as a Service which features of an advanced enterprise-grade SIEM, coupled with comprehensive ELK Stack Event-Logging and combined with the only commercially available “Real-Time” CDM Cybersecurity product as a single solution.
- Anamo CDM “Real-Time” Cybersecurity,
- NIST 800-53/171 Governance, Risk & Compliance Management (GRC App)
- Security Operations Center (SOC) as a Managed Service on a 24/7 basis.
- Event Log Collection, Monitoring & Alert Notification
Continuous Diagnostics & Mitigation (CDM) Cybersecurity Platform
“Anamo is Real-Time Insider-Threat detection, Software Vulnerability Monitoring, Alert Notification and Forensics”
Having a security operations center (SOC) has become an absolute necessity for implementing an around-the-clock cybersecurity threat analytics capability. Anamo provides SOC services as a fully managed solution and offers the latest Continuous Diagnostics and Mitigation (https://www.dhs.gov/cdm) capabilities to the SOC, all while providing exception insight into Forensics, Software Vulnerability, finite Insider-Threat analytics and a host of commonly tracked services within our comprehensive SIEM solution.
Anamo delivers 24/7/365 threat lifecycle management to minimize damage caused by successful attacks and prevents the spread and chaos associated to any compromise. A managed SOC is the just-right solution for organizations that cannot justify the overwhelming expenses of a formal SOC and cannot tolerate the inadequate protection provided by an informal SOC.
One of the most frustrating challenges when it comes to cybersecurity is keeping track of subtle changes. Server filesystems pose thousands of files, directories, and other resource risks. Keeping track of when those changes occur is both overwhelming and incredibly important.
What if, though, software that ran 24/7 did it for you, keeping an eye on the entire state of your filesystem at different dates and times. That would allow you to know what users and groups owned what resources and what permissions were set to. Anamo is an incredible search engine and alerting tool for keeping track of the vast tree of a Linux or Windows server systems.
The Anamo Continuous Diagnostics & Mitigation (CDM) platform is the ideal technology for building a SOC to provide SIEM capabilities in near Real-Time. Organizations that adopt this strategy can achieve immediate and ongoing cost savings as compared to adopting any other SOC model. This strategy also leads to a material reduction in risk for the organization.
Specific ways in which the Anamo CDM Managed Enterprise platform benefits organizations include the:
- Anamo takes care of the “heavy lifting,” eliminating any need to run intensive software or impose any performance burden on our customers’ IT environment. Data is received by Anamo at regular time-based intervals, and upon arrival, vast quantities of data are parsed to extract relevant cybersecurity information, bring it to the surface, and present actionable information. The “end” result is a much more informed perspective on your organization’s cybersecurity, the type that enables more intelligent and more real-time decision-making. Additional SOC attributes, services and considerations include:
- Anamo uses advanced capabilities for threat detection and analysis, such as user and entity behavior analytics, that can find and understand the significance of many types of threats that cannot easily be detected by other means. This is particularly helpful for identifying insider threats attempting to access and steal sensitive data.
- Anamo automates incident response orchestration so that all people involved in incident response have immediate access to necessary information. Anamo’s security automation and orchestration capabilities significantly improve the efficiency and effectiveness of incident identification, notification, forensics and response.
Soc as a Service with integrated compliance:
NIST 800-53/171 Government Regulatory Compliance Management
US ProTech’s unique software “The GRC App” is the ONLY commercially available NIST 800 Assessment application and reporting tool that is pre-populated with all essential policies & procedures, incident mgt, document, mgt. project mgt. user/team mgt. and much more. For a complete understanding of the Governance Risk & Compliance platform visit: https://grc.usprotech.com/
Soc as a Service with integrated SIEM and ELK Stack Event Logging
Asset Discovery
- What instances are running in my cloud environments?
- What devices are on my physical and virtual networks?
- What vulnerabilities exist on the assets in my cloud and network?
- What are my users doing?
- Are there known attackers trying to interact with my cloud and network assets?
- Are there active threats on my cloud and network assets?
Vulnerability Assessment
- Leverage intrusion detection for any environment with built-in cloud IDS, network IDS, and host-based IDS (including File Integrity Monitoring (FIM))
- Use the Kill Chain Taxonomy to quickly assess threat intent and strategy
- Make informed decisions with contextual data about attacks, including a description of the threat, its method and strategy, and recommendations on response
- Use automatic notifications so you can be informed of key threats as they happen
- Work more efficiently with powerful analytics that uncover threat and vulnerability details – all in one console
- Detect Unauthorized Access Attempts
- Identify Anomalous Activities
- Know When and Who Accessed & Changed Critical Files with File Integrity Monitoring (FIM)
- Protect the Integrity of your Assets and Data
- Monitor file access to sensitive data in your CDE and know when changes are made to critical files
- Investigate FIM-triggered alarms to identify who accessed, downloaded, and modified critical files
- Easily report out on FIM activities using the built-in PCI DSS reports and create your own custom views and reports for review
- Identify assets in your cloud and on-premises environments with built-in asset discovery and inventory tools
- Schedule scans and monitor your assets for new vulnerabilities and weaknesses
- Know which vulnerabilities are being exploited with built-in intrusion detection
Intrusion Detection
- Automate threat hunting everywhere modern threats appear
- Investigate threats faster with contextual information about the endpoint
- Automatically prioritize threats for faster, more effective incident response
- Accelerate incident investigation and response with built-in orchestration
Behavioral Monitoring
- Service & Infrastructure Monitoring
- Provides continuous monitoring of services run by specific systems. On a periodic basis, or on demand, the device is probed to confirm that the service is still running and available.
- NetFlow Analysis
- Performs network behavior analysis without needing the storage capacity required for full packet capture.
- NetFlow analysis provides the high-level trends related to what protocols are used, which hosts use the protocol, and the bandwidth usage.
- This information can then be accessed in the same interface as the asset inventory and alarm data to simplify incident response.
- Generate alarms and get alerted when your NetFlow goes above or below certain thresholds.
- Network Protocol Analysis / Packet Capture
- Allows security analysts to perform full protocol analysis on network traffic enabling a full replay of the events that occurred during a potential breach.
- This level of network monitoring can be used to pinpoint the exploit method used or to determine what specific data was exfiltrated.
SIEM/Event Correlation
- See the Advantages of All-in-One Security Essentials Versus Traditional SIEM
- Save Time and Money in Integrating Multiple Third-Party Security Tools
- Start Detecting Threats on Day One with Pre-Written Correlation Rules
- Get Continuous Security Intelligence Delivered from Anamo CDM Security Labs
- Discover a Smarter Way to Prioritize Your Incident Response
- Use the Kill Chain Taxonomy to Quickly Assess Threat Severity, Intent, and Strategy
- Remediation Recommendations and Noise Reduction Help You Work More Efficiently
- Investigate Threats Deeper with Advanced Security Analytics
- Search and Analyze Security Data in Highly Granular Ways
- Dive Deep into Alarms with Unified Asset, Vulnerability, and Event Data
- Stay Vigilant with Threat Intelligence Updates from Anamo CDM Security Labs
- Receive Continually Updated Correlation Rules and Threat Context from Anamo CDM Security Labs
Threat Intelligence
- Save Time and Money with All-in-one Security Essentials
- Alleviate integration headaches with a complete unified security platform
- Easily collect data from third-party applications, systems, and devices to feed the SIEM event correlation
- Start detecting threats immediately with 3000+ correlation rules delivered out of the box
- Continuous Threat Intelligence Delivered as Threats Change
- Keep pace with attackers with correlation rules and security updates
- Focus on the Threats That Matter Right Now
- Prioritize your response efforts with automated risk assessment and alarm escalation
- Quickly assess your threat exposure with a cyber kill chain prioritization strategy
Threat Detection
- Focus on the Threats That Matter Right Now
- Quickly assess threats with automated alert prioritization
- Make informed decisions with full details on every alarm, including a description of the threat, its method and strategy, and recommendations on response
- Get Compete Threat Visibility with All-in-One Security Essentials
- Achieve multi-layered threat detection for your on-premises and cloud environments using the USM platform’s built-in host-, network-, and cloud-based intrusion detection systems and endpoint detection capabilities
- Easily search and analyze threats with a consolidated view of your assets, vulnerabilities, and malicious activities in your environment
- Eliminate your security blind spots by aggregating and correlating events from all your devices, servers, endpoints, and applications, as well as monitoring user and administrator activities
- Stay Vigilant with Continuous Threat Intelligence Delivered
- Receive continuous, curated threat intelligence delivered automatically to the USM platform
- Stay ahead of emerging threats with correlation rules that are continually and automatically updated with the latest threat intelligence
- Detect and Respond to Ransomware Threats Quickly with Unified Security Management
- Near Real-time threat detection with built-in essential security capabilities
- Coordinated incident response with integrated analysis and reporting
- Monitor Every Environment with Comprehensive Intrusion Detection
- Unified security monitoring of Office 365 and other cloud apps to detect ransomware threats early on
- Cloud Intrusion Detection (AWS and Azure) – alert on critical events within your AWS and Azure environments consistent with ransomware indicators.
- Network Intrusion Detection – alert on known ransomware communication activity based on continuous updates
- Host Intrusion Detection – alert on known ransomware attack activity detected on the critical servers across all your environments
Conclusion about Cybersecurity and Service:
In today’s modern and fast paced business environment there are few companies in the United States that remain focused on “service.” So, US ProTech askes the question… “Are you 100% satisfied with the Service you receive from your technology providers?”
US ProTech is technically capable and ready to serve you. With 20 consecutive years of providing cybersecurity services, risk assessments, security audits, penetration testing, blue-team defenses, and the development of advanced cybersecurity and compliance software applications, we understand and deliver “service.” The very idea of Software as a Service has in some cases has caused the abuse of service in that in many cases it provides none.
While the term service is thrown around by companies and rarely delivered, service is exactly what US ProTech guarantees to each of its customers. If you’d like to hear what our clients say…. all you need do is ask any US ProTech client about their opinion and their experience with US ProTech. Then, contact us so that you can experience the “service” in our Security Operations Center (SOC) as a Service offering.
For additional information contact:
US ProTech | www.USProTech.com
Anamo | www.Anamo.io